Scientists Hack Teleoperated Surgical Robot To Expose Security Flaws
A team of computer engineers has experimented with different kinds of cyberattacks and released series of studies that highlight some of the problems that can arise when using a telerobotic surgical device on an open network. Though they suggest some solutions, the team’s primary goal was to raise awareness of the potential problems facing teleoperated surgical procedures.
In 2000, the FDA cleared the first completely robotic surgical system for sale in the United States. Since then, the use of robotic systems in the operating room has been growing steadily. However, most of these systems are operated on a closed network that is difficult to hack.
A team of scientists from the University of Washington (UW) anticipates circumstances where these robotic surgeries will have to use more open networks such as remote battlefield, an underdeveloped rural location, or for a patient who has been quarantined because of an infectious disease.
“In an ideal world, you’d always have a private network and everything could be controlled, but that’s not always going to be the case. We need to design for and test additional security measures now before the next generation of telerobots are deployed,” said Howard Chizeck, co-director of the UW BioRobotics Lab, in an article published by UW Today.
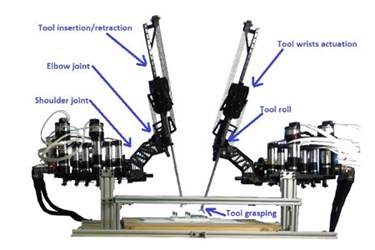
Open networks leave the technology especially vulnerable to several different kinds of common cyberattacks, say experts. In a series of studies, the team tested Raven II, an open-source, robotic-assisted surgical device built by UW electrical engineering professors, which was designed to access an open network.
In the first study, the team experimented to see if they could hijack the machine and input different commands using a “man in the middle” approach, where an attacker alters information sent between two parties — in this case, the operator and the robot — without them knowing it. While using the machine to move rubber stoppers around a peg board, the engineers discovered that they could override many of the robots functions and even make it shut down completely.
A second study looked specifically at denial-of-service (DoS) attacks, where a batch of nonsense data is introduced to the information flowing between the operator and the robot. These attacks made the machine hard to handle and jerky, which could be extremely dangerous during surgery.
The team also experimented with several tried-and-true methods for deflecting hijackers such as encryption and operator verification, but said that these methods must be refined further to be dependable enough for safe surgical procedures.
More than anything else, the team is seeking to raise awareness of the serious security issues that face the growing field of telerobotics in the hopes that more cybersecurity experts can become involved in refining the technology.
Tamara Bonaci, the lead author of the studies, said, “We want to make the next generation of telerobots resilient to some of the threats we’ve detected without putting an operator or patient or any other person in the physical world in danger.”
Image credit: University of Washington
